Argocd Credentials Template - Web argo cd is a declarative, gitops continuous delivery tool for kubernetes. Web starting with openshift gitops v1.3, which uses argo cd v2, repository access and authentication is done by storing the github token in a kubernetes secret in. Web in order for argo cd to use a credential template for any given repository, the following conditions must be met: The feature is disabled by default because badge image is available to any user without. Application definitions, configurations, and environments should be declarative and version controlled. Web to use secrets to create private repositories in argocd, you will need to create a secret in your kubernetes cluster that contains the credentials required to. Argo cd can display a badge with health and sync status for any application. Web for example, we can install credentials that are used to authenticate with private git or helm repositories by placing them in the chart template/ directory. Web argocd accomplishes cd methodologies by using git repositories as a source of truth for kubernetes manifests that can be specified in a number of ways. You can also set up credentials to serve as templates for connecting repositories, without having to repeat credential configuration.
Certificate Of Ordination Template
Web argo cd is a declarative, gitops continuous delivery tool for kubernetes. You can also set up credentials to serve as templates for connecting repositories, without having to repeat credential configuration. Web the error message you see comes from k8s api when it tries to create the secret for your credential template, and the git@ string should definitely not part.
Radio Media Credentials Template Print templates, Radio, Templates
Web to use secrets to create private repositories in argocd, you will need to create a secret in your kubernetes cluster that contains the credentials required to. Application definitions, configurations, and environments should be declarative and version controlled. The repository must either not be configured at all, or if. Application deployment and lifecycle management. The repository must either not be.
ArgoCD二:一个完整的CICD流程例子 我爱西红柿
Credential templates are available only via declarative setup, see repository credentialsin operator manual. The repository must either not be configured at all, or if. For example, if you setup credential templates for the url prefix. Application definitions, configurations, and environments should be declarative and version controlled. Web for example, we can install credentials that are used to authenticate with private.
Credentials
Web in order for argo cd to use a credential template for any given repository, the following conditions must be met: For example, if you setup credential templates for the url prefix. Web argocd accomplishes cd methodologies by using git repositories as a source of truth for kubernetes manifests that can be specified in a number of ways. The repository.
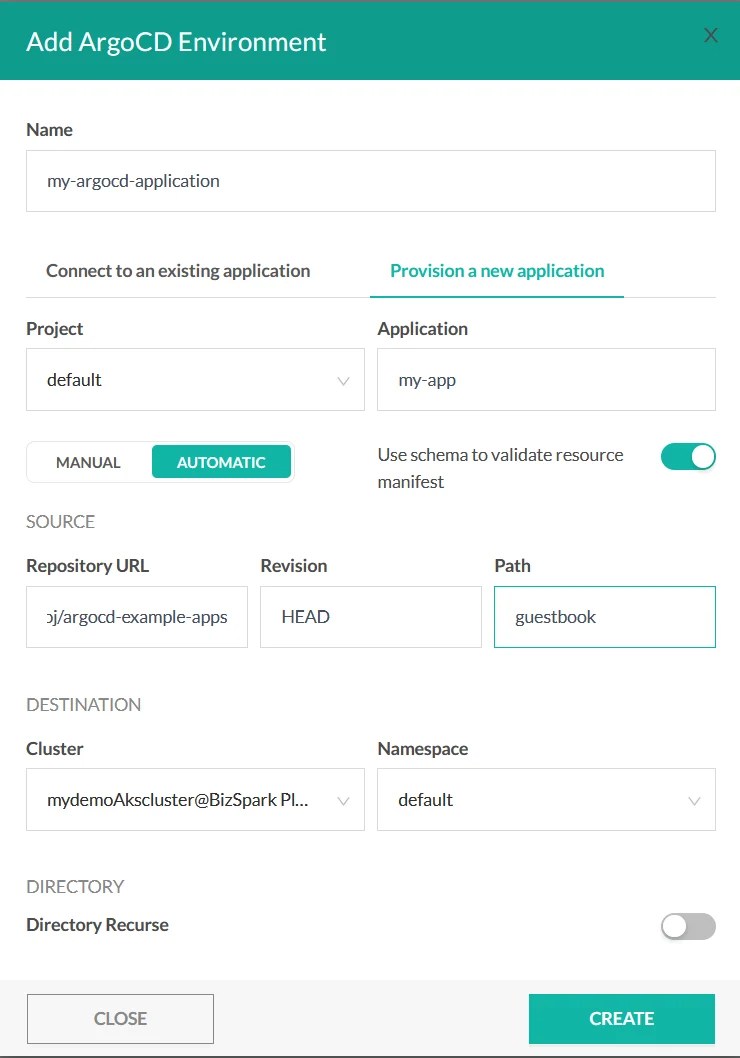
ArgoCD integration · Codefresh Docs
Application definitions, configurations, and environments should be declarative and version controlled. Credential templates are available only via declarative setup, see repository credentialsin operator manual. Web the error message you see comes from k8s api when it tries to create the secret for your credential template, and the git@ string should definitely not part of it. Web argo cd is a.
ArgoCD a Helm chart deployment, and working with Helm Secrets via AWS KMS
Web to use secrets to create private repositories in argocd, you will need to create a secret in your kubernetes cluster that contains the credentials required to. Web argocd accomplishes cd methodologies by using git repositories as a source of truth for kubernetes manifests that can be specified in a number of ways. Web credential templates can carry the same.
10x28mm Delta Green FBI Credentials
Credential templates are available only via declarative setup, see repository credentialsin operator manual. The repository must either not be configured at all, or if. Web argocd accomplishes cd methodologies by using git repositories as a source of truth for kubernetes manifests that can be specified in a number of ways. Web for example, we can install credentials that are used.
CREDENTIALS & CERTIFICATE JP Trading Co
The repository must either not be configured at all, or if. Web for example, we can install credentials that are used to authenticate with private git or helm repositories by placing them in the chart template/ directory. Application deployment and lifecycle management. Application definitions, configurations, and environments should be declarative and version controlled. Credential templates are available only via declarative.
Apathy Media Credentials Template
Web argo cd is a declarative, gitops continuous delivery tool for kubernetes. The feature is disabled by default because badge image is available to any user without. The repository must either not be configured at all, or if. The repository must either not be configured at all, or if. Application definitions, configurations, and environments should be declarative and version controlled.
CREDENTIALS
Application definitions, configurations, and environments should be declarative and version controlled. The feature is disabled by default because badge image is available to any user without. Web for example, we can install credentials that are used to authenticate with private git or helm repositories by placing them in the chart template/ directory. Web to use secrets to create private repositories.
The repository must either not be configured at all, or if. Web argocd accomplishes cd methodologies by using git repositories as a source of truth for kubernetes manifests that can be specified in a number of ways. Application deployment and lifecycle management. The repository must either not be configured at all, or if. Web argo cd is a declarative, gitops continuous delivery tool for kubernetes. You can also set up credentials to serve as templates for connecting repositories, without having to repeat credential configuration. Web in order for argocd to use a credential template for any given repository, the following conditions must be met: Web the error message you see comes from k8s api when it tries to create the secret for your credential template, and the git@ string should definitely not part of it. For example, if you setup credential templates for the url prefix. Web for example, we can install credentials that are used to authenticate with private git or helm repositories by placing them in the chart template/ directory. Web in order for argo cd to use a credential template for any given repository, the following conditions must be met: The feature is disabled by default because badge image is available to any user without. Web starting with openshift gitops v1.3, which uses argo cd v2, repository access and authentication is done by storing the github token in a kubernetes secret in. Web to use secrets to create private repositories in argocd, you will need to create a secret in your kubernetes cluster that contains the credentials required to. Credential templates are available only via declarative setup, see repository credentialsin operator manual. Web credential templates can carry the same credentials information as repositories. Argo cd can display a badge with health and sync status for any application. Application definitions, configurations, and environments should be declarative and version controlled.
Web In Order For Argo Cd To Use A Credential Template For Any Given Repository, The Following Conditions Must Be Met:
You can also set up credentials to serve as templates for connecting repositories, without having to repeat credential configuration. Web argocd accomplishes cd methodologies by using git repositories as a source of truth for kubernetes manifests that can be specified in a number of ways. Argo cd can display a badge with health and sync status for any application. Web starting with openshift gitops v1.3, which uses argo cd v2, repository access and authentication is done by storing the github token in a kubernetes secret in.
The Repository Must Either Not Be Configured At All, Or If.
For example, if you setup credential templates for the url prefix. Web credential templates can carry the same credentials information as repositories. Application deployment and lifecycle management. Web for example, we can install credentials that are used to authenticate with private git or helm repositories by placing them in the chart template/ directory.
The Repository Must Either Not Be Configured At All, Or If.
Application definitions, configurations, and environments should be declarative and version controlled. Web in order for argocd to use a credential template for any given repository, the following conditions must be met: Web argo cd is a declarative, gitops continuous delivery tool for kubernetes. Credential templates are available only via declarative setup, see repository credentialsin operator manual.
The Feature Is Disabled By Default Because Badge Image Is Available To Any User Without.
Web the error message you see comes from k8s api when it tries to create the secret for your credential template, and the git@ string should definitely not part of it. Web to use secrets to create private repositories in argocd, you will need to create a secret in your kubernetes cluster that contains the credentials required to.